Adaptive Sandbox
Adaptive Sandbox is OPSWAT’s evasive malware analysis technology that uses emulation-based dynamic analysis to inspect advanced threats across cloud, on-prem, and air-gapped environments. It combines adaptive emulation with static and behavioral analysis to extract actionable IOCs and support SOC, threat intelligence, and hunting workflows at scale.
- Resilienza contro l'evasione
- Analisi di grandi volumi
- CIOE attivabili
OPSWAT è affidabile per
Motore di emulazione a livello di istruzioni
Elude le tecniche anti-VM
25k+
Server
120+
Tipi di file supportati
circa 10 secondi
Analisi rapida
900+
Indicatori comportamentali
Esportazioni in formato MISP, STIX e JSON
Implementazioni Cloud, in locale e con isolamento fisico
Il malware moderno è stato progettato per eludere i sistemi di rilevamento
Le sandbox tradizionali basate su macchine virtuali presentano difficoltà in termini di prestazioni, scalabilità e tecniche avanzate di anti-analisi.
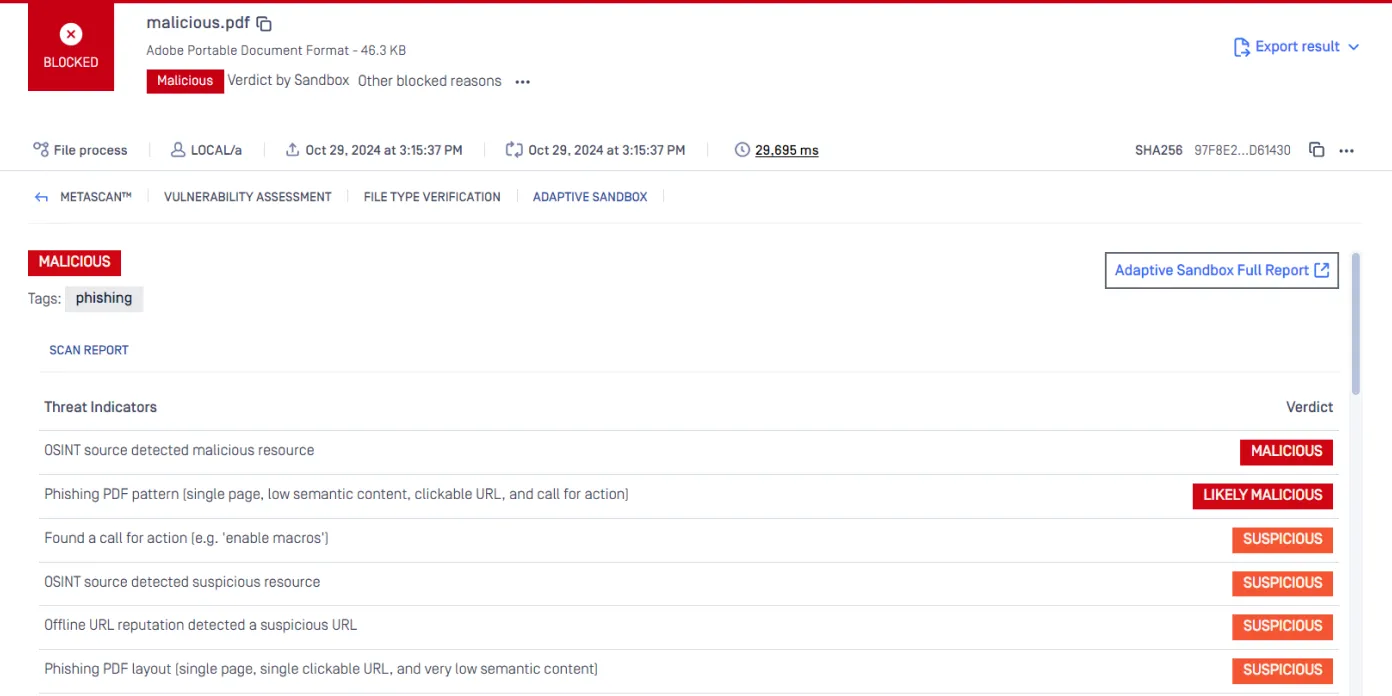
Il malware evasivo nasconde il proprio comportamento
Le minacce avanzate rilevano le macchine virtuali, ritardano l'esecuzione, verificano la geolocalizzazione o si attivano solo in determinate condizioni, rendendo i sandbox tradizionali incapaci di rilevare il comportamento effettivo durante l'esecuzione.
L'utilizzo del sandboxing rallenta il flusso dei file
Le "detonation farm" basate su macchine virtuali creano colli di bottiglia, costringendo le organizzazioni a scegliere tra l'ispezione approfondita e la velocità operativa a livello perimetrale o nelle pipeline del SOC.
Gli avvisi mancano di profondità comportamentale
Le ispezioni statiche e i controlli della reputazione si limitano agli hash e ai domini, fornendo poche informazioni sul contesto riguardo alle intenzioni degli autori degli attacchi, agli strumenti utilizzati o alle relazioni tra le campagne.
Adaptive che
costringe il malware a rivelarsi
Analisi dinamica a livello di istruzione in grado di adattarsi alle diverse esigenze senza compromettere la visibilità, la velocità o la flessibilità di implementazione.
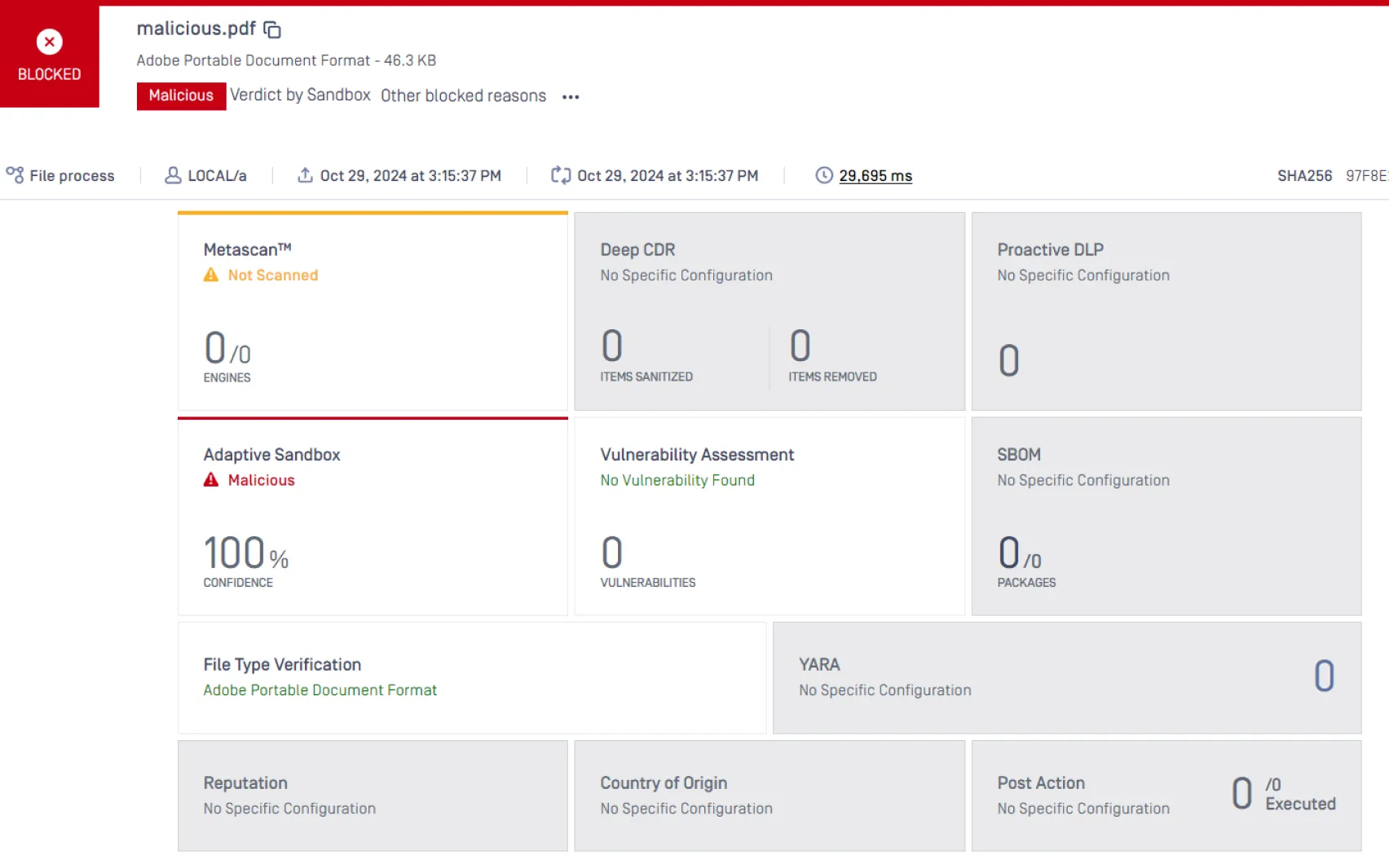
Dall'invio della documentazione al verdetto comportamentale
Una pipeline di analisi statica e dinamica a più livelli progettata per individuare tecniche di elusione e attacchi in più fasi.
Caratteristiche principali
Architettura resistente all'evasione
L'emulazione a livello di istruzioni riduce l'esposizione alle tecniche di identificazione delle macchine virtuali (VM), quali lunghi periodi di inattività, controlli di geofencing, rilevamento della sandbox ed esecuzione ritardata del payload.
Elevata capacità di elaborazione
Elabora oltre 25.000 analisi al giorno per server grazie all'ispezione dinamica "fast-pass", supportando ambienti su scala aziendale senza colli di bottiglia nelle prestazioni.
Modello di implementazione flessibile
Implementazione in ambienti cloud-native, on-premise, ibridi o completamente isolati, nel rispetto dei requisiti normativi e dei vincoli operativi di elevata sicurezza.
Copertura Adaptive
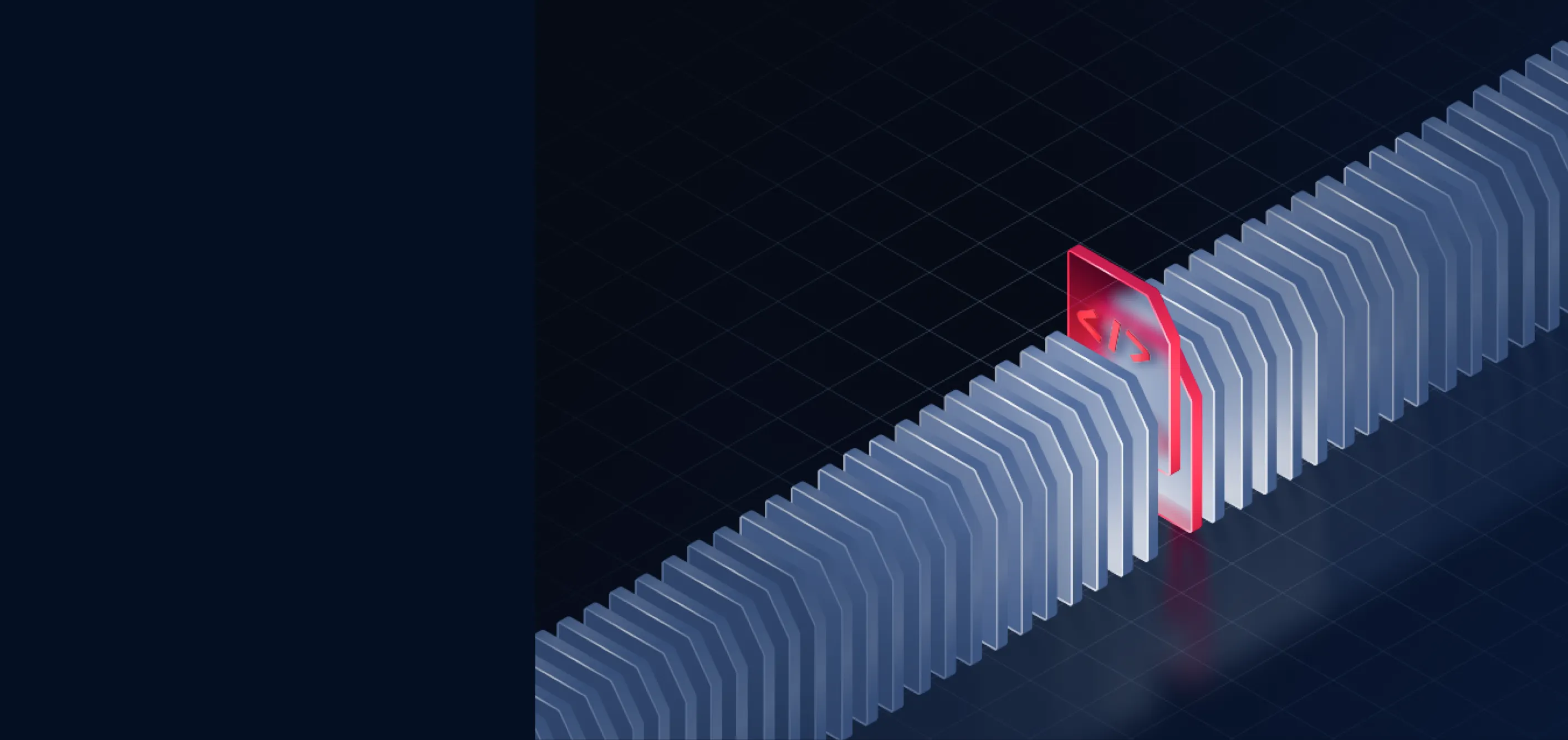
Adaptive Sandbox progettato per contrastare le moderne tattiche di elusione, tra cui:
- Geofencing e verifica della posizione
- Cicli di sospensione prolungata ed esecuzione ritardata
- Codici VBA offuscati e payload OOXML danneggiati
- File eseguibili compressi o gonfiati
- Shellcode e payload solo in memoria
- Caricatori e scaricatori multistadio
Manipolando il flusso di esecuzione a livello di istruzione, il motore mette in evidenza comportamenti che potrebbero non verificarsi mai in ambienti basati su macchina virtuale.
Distribuire ovunque, integrare ovunque
Una soluzione scalabile e completa per la sicurezza dei file che si integra perfettamente e segue i vostri file ovunque vadano.
Risorse

MetaDefender

2025 Rapporto OPSWAT sul panorama delle minacce