File security at the network edge only works if it can keep up. When a secure web gateway is inspecting every file passing through (via downloads, uploads, web content) the security layer needs to stay transparent: invisible to users, consistent under load, and not the reason anything surfaces in a compliance review.
These are operational realities that become harder to manage as traffic grows, access policies tighten, and audit scope expands. MetaDefender ICAP Server 5.13.0 addresses three of them directly.
Handling More Traffic Without Adding Infrastructure
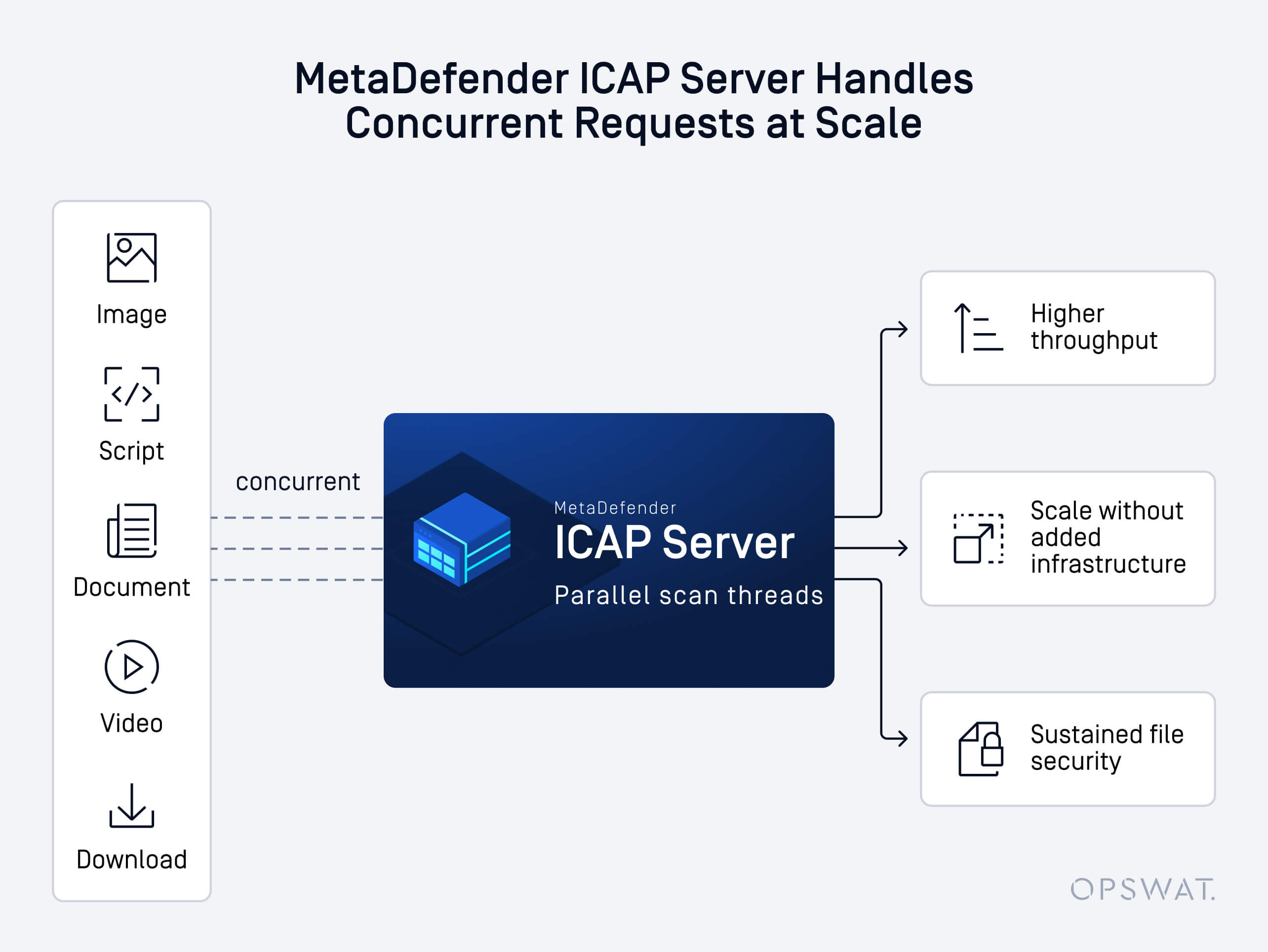
One thing that often overwhelms teams when they instrument ICAP traffic: a single user browsing the web through a secure gateway may generate dozens, or even hundreds of ICAP requests, in rapid succession. Every image, script, document, and download is a separate file inspection request hitting the server concurrently.
At moderate traffic, most deployments handle this without issue. As concurrency increases, the bottleneck can typically be found in the surrounding operations: writing results to the database, flushing log output, managing thread state.
At high concurrency, processing requests and recording results in the same pipeline becomes the bottleneck, limiting throughput precisely when demand is highest.
MetaDefender ICAP Server 5.13.0 decouples those operations. Scan threads now hand off database writes and log output to dedicated background processes the moment a scan completes, then immediately pick up the next request. The outcome is that inspection throughput scales more cleanly with traffic, without adding hardware or expanding thread pool sizes.
Most relevant for: Teams running secure web gateways, where a single user session can generate dozens of concurrent file inspection requests. The higher the traffic, the more this change matters.
SSO Logout That Covers the Full Session Lifecycle
SAML Single Logout is one of the more commonly incomplete aspects of SSO implementations. Teams typically invest in configuring authentication with trust establishment, assertion validation, and session creation. The logout side tends to receive less attention, and partial logout can appear to work correctly on the surface.
The gap is worth understanding: when a user signs out of an application that only clears its local session, the IdP session remains active. That session can be silently reused. A user returning to the login page may be re-authenticated automatically, without re-entering credentials and without MFA. In environments with shared workstations or elevated-privilege accounts, that's an access path that persists beyond intent.
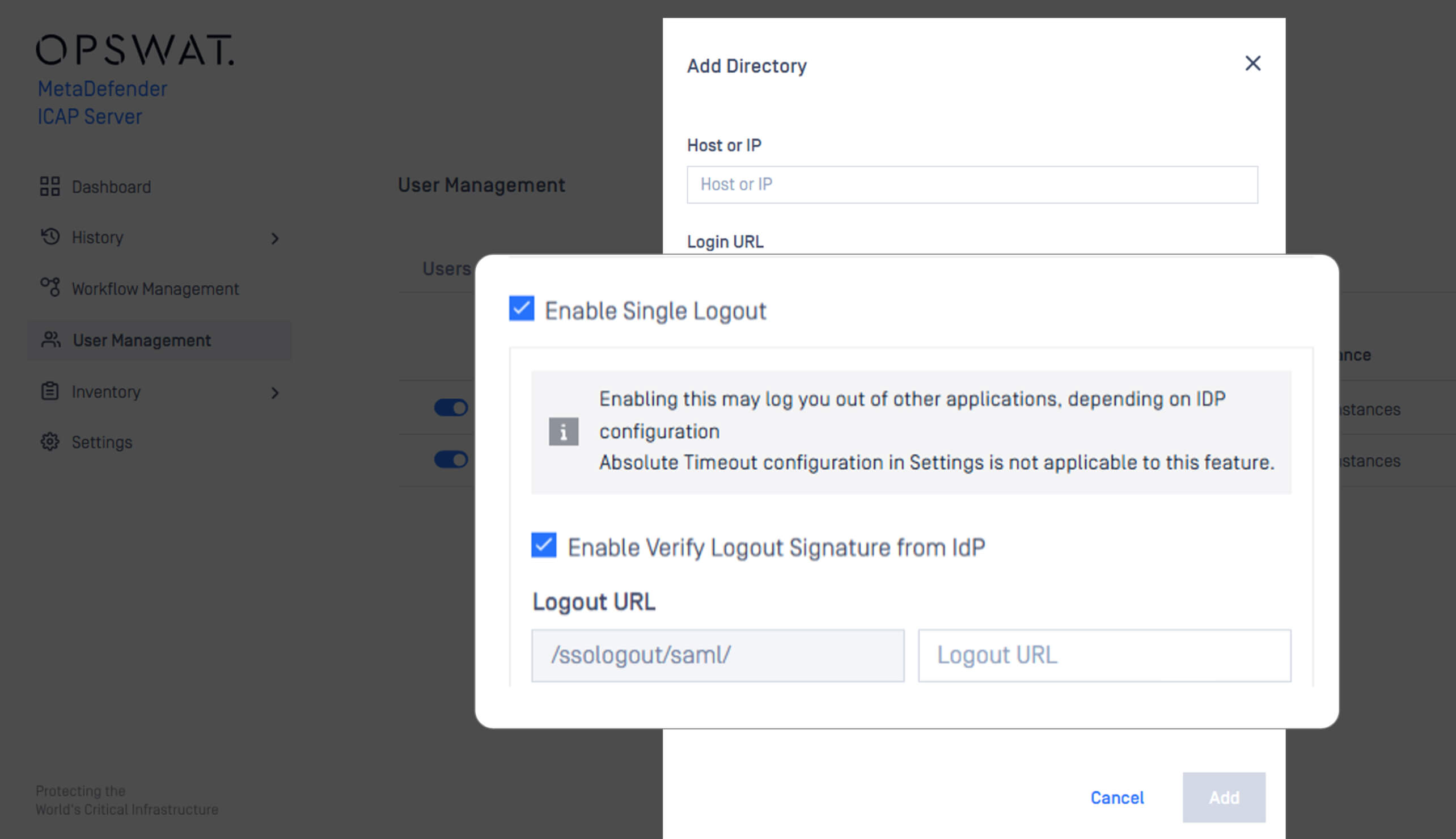
MetaDefender ICAP Server 5.13.0 adds full SAML Single Logout (SLO) support. On sign-out, MetaDefender ICAP Server sends a logout request directly to the identity provider, terminates the session at the source, and requires fresh authentication before access is restored. Post-logout redirect behavior is also configurable.
For teams subject to access control audits or zero-trust policies, this brings session termination in line with what a complete SAML implementation requires.
When Scan Logs Become a Privacy Concern
Security teams spend most of their attention on what enters the environment — what gets blocked, what gets flagged, what gets logged for review. Less attention typically goes toward what the security tooling itself accumulates over time.
As part of its processing history, MetaDefender ICAP Server retains request URLs, and in many deployments, those URLs carry more than just a file path. Query parameters appended during normal web activity can include user-identifiable data that falls under GDPR, CCPA, or sector-specific privacy regulations.
This kind of exposure tends to surface during audits, when the scope of what's stored turns out to be broader than expected.
MetaDefender ICAP Server 5.13.0 introduces an optional URL masking setting that strips sensitive query parameters from the processing history before they are written to storage.
Most relevant for: Organizations subject to GDPR, CCPA, or sector-specific data privacy regulations — particularly those where web application URLs regularly carry user-identifiable parameters.
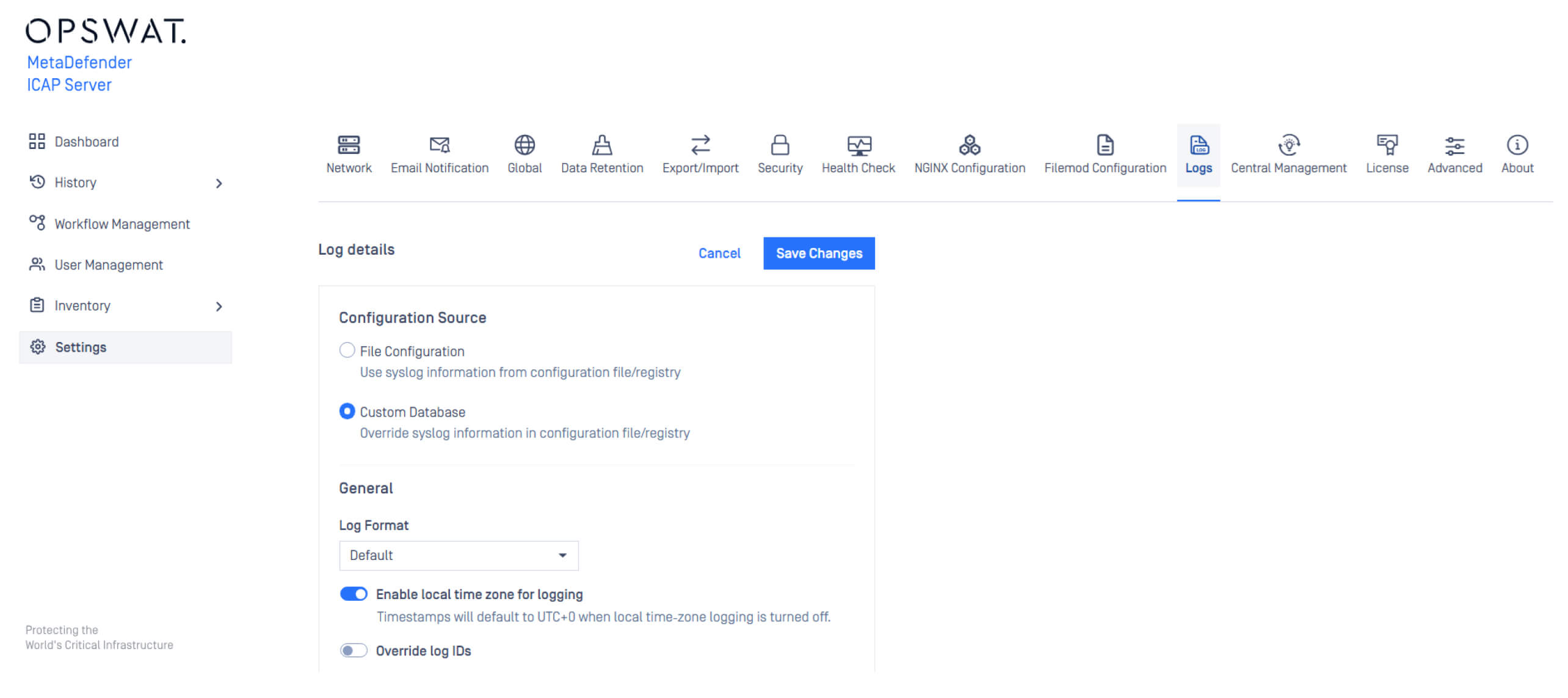
Advanced Log Configuration via Web Console
Settings such as local time zone, Common Event Format (CEF), product logs, and syslog settings are now all configurable through the web console — no manual file editing required.
Also in This Release
Security Library Upgrades
Updated PostgreSQL (v16.13), OpenSSL (v3.4.4), Angular (v19.2.19), gRPC (v1.71.1), and Curl (v8.18.0), with additional hardening measures applied across the product.
Faster Processing History Exports
Large scan history databases could time out during export. The export process has been optimized to handle high-volume datasets without hitting those limits — relevant for teams relying on processing history for compliance reporting or post-incident review.
Corrected Handling of Non-Standard Content-Encoding Headers
If a request carries an encoding header the server doesn't recognize, the file may reach the scan engine in an unexpected state or not be inspected as intended. MetaDefender ICAP Server 5.13.0 adds handling for non-standard encoding values that appear in real-world traffic, ensuring consistent inspection coverage.
Built to Protect What Enters Your Environment
MetaDefender ICAP Server secures files at the network perimeter, before they enter your organization and reach users, applications, or storage. That's where threats are most efficiently intercepted, and where gaps in reliability or compliance have the most impact.
MetaDefender ICAP Server 5.13.0 focuses on making that layer more dependable: throughput consistency under load, session integrity across the full SSO lifecycle, and privacy-safe handling of what gets retained. The core protection capabilities, including Metascan Multiscanning powered by multiple anti-malware engines and AI, Deep CDR™ Technology, and File-Based Vulnerability Assessment, remain unchanged. This release strengthens the infrastructure that supports them
Aggiorna ora
MetaDefender ICAP Server 5.13.0 is available now. Existing customers can download the latest release from the My OPSWAT Portal. For full release notes and upgrade instructions, visit the OPSWAT Documentation.
Not yet using MetaDefender ICAP Server? Contact our team to learn how it can protect your file traffic at the edge.
MetaDefender ICAP Server protects organizations against file-based threats at the network perimeter, across load balancers, web application firewalls, proxies, and any other ICAP-enabled device.

