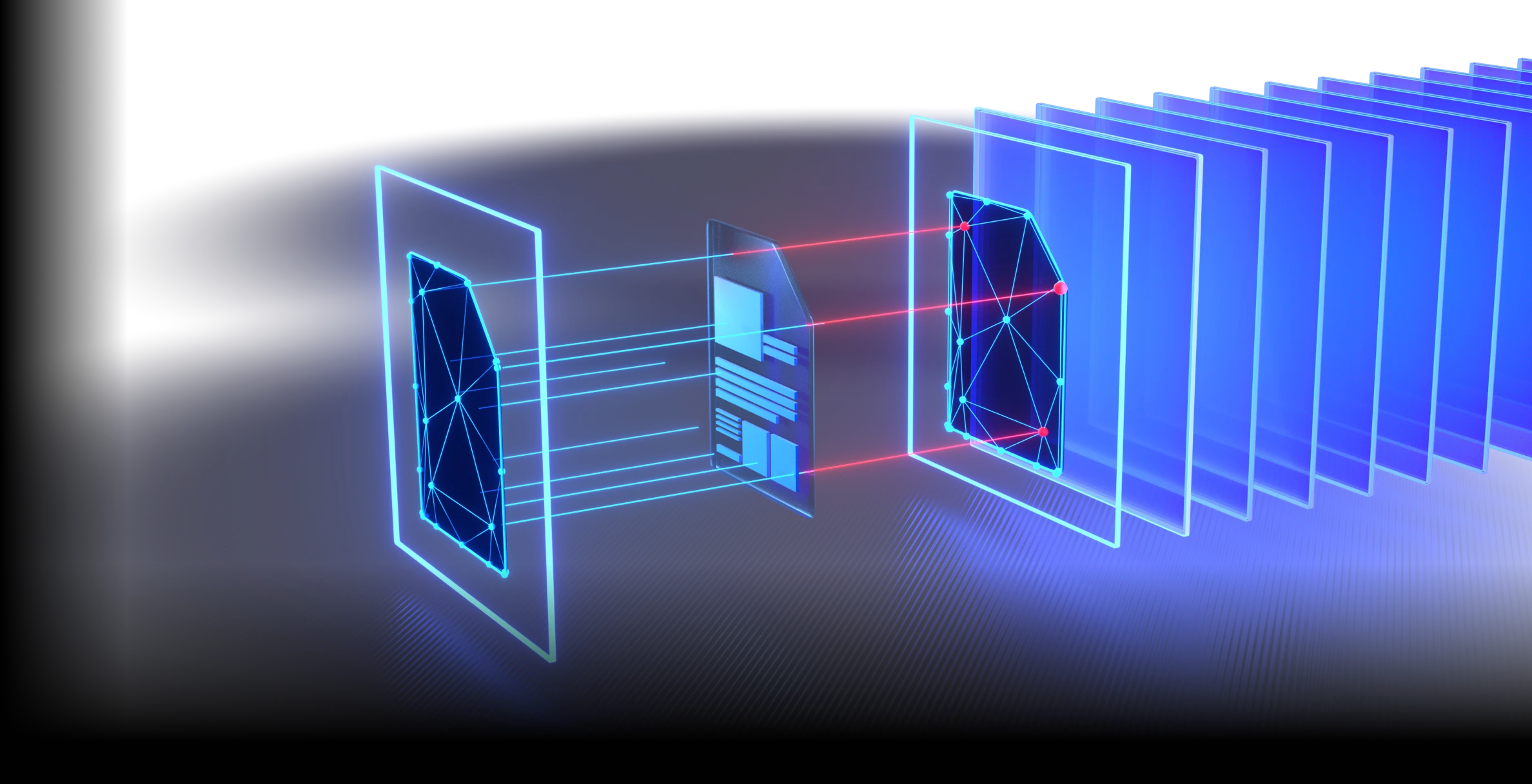
MetaDefender® Platform Guardrails for LLMs
Secure files, content, and data before they reach your LLM. Stop file level threats, reduce RAG poisoning risk, enforce one-way transfer, and protect your AI investment.
- Prevention First Security
- Sanificazione profonda dei file
- Hardware Enforced Isolation
OPSWAT è affidabile per
The New AI Attack Surface
File-Borne Malware in AI Pipelines
Malicious payloads hide inside common business files like PDFs, Office documents, and archives. Typical AI guardrails focused on text do not neutralize embedded file-level risks.
Knowledge Manipulation Through Untrusted Documents
Malicious or deceptive documents can enter retrieval pipelines, get indexed, and silently influence model outputs over time, turning the knowledge base into an attack vector.

Sensitive Data Exposure to AI Systems
Users upload financial data, source code, credentials, and customer records into AI workflows. Once exposed to external models or poorly governed services, organizations face loss of data control and potential regulatory liability.

Embedded Prompt Injection Inside Files
Instructions hidden inside uploaded documents, rather than typed directly into chat, can manipulate model behavior and downstream tools when retrieved through RAG or agent workflows.

Unknown and Zero-Day File-Based Threats
AI workflows encourage massive content ingestion, increasing exposure to previously unseen threats. Detection alone is not enough. Prevention must occur before content enters the pipeline, or organizations risk regulatory penalties and reputational harm from undetected breaches.
Prevention First Security for Enterprise AI
MetaDefender Core applies a prevention-first model to AI content flows and secures what enters the model, what gets indexed, and what crosses trust boundaries.
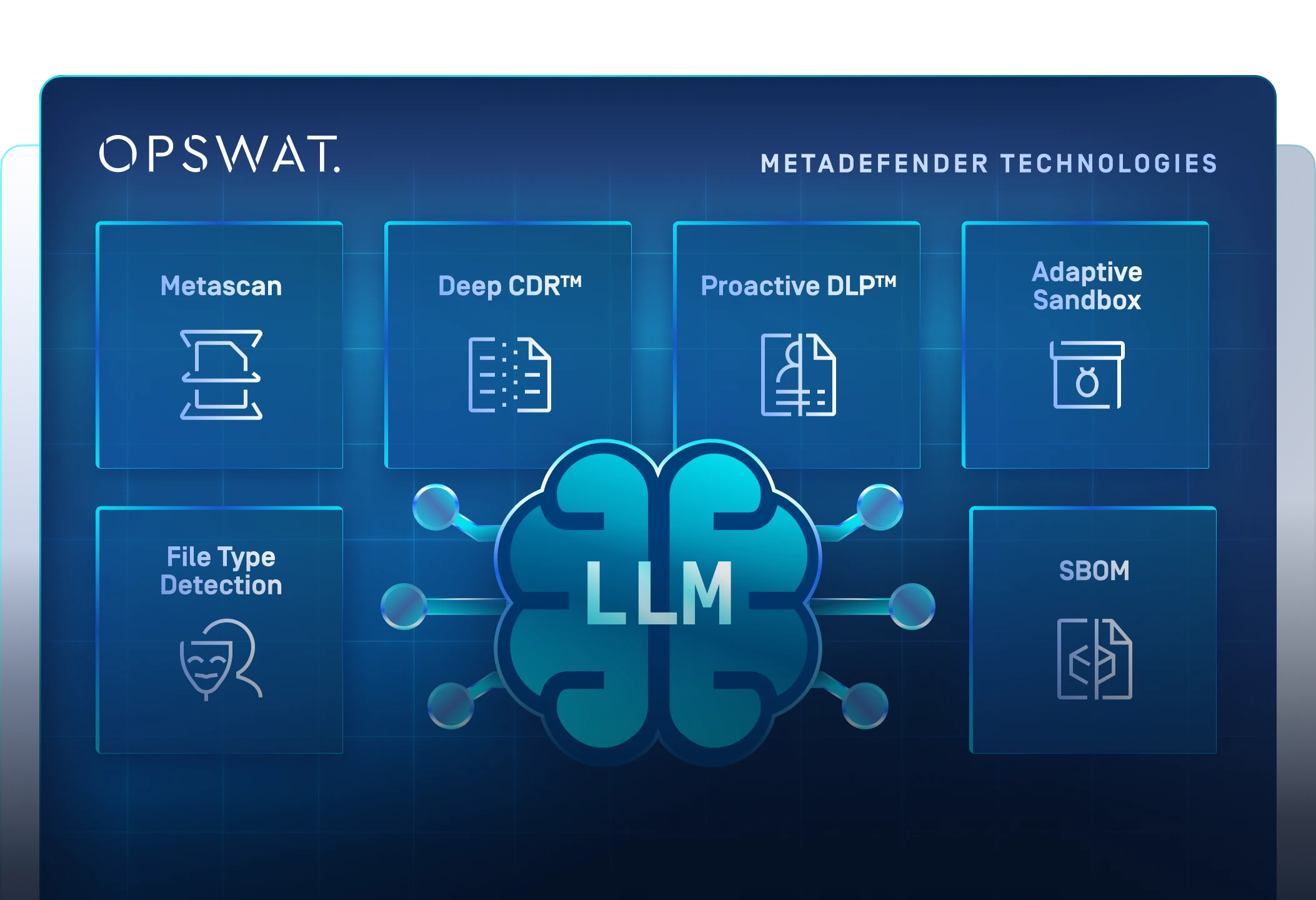
Caratteristiche
Progettato per le previsioni,
Progettato per la velocità
- Analisi approfondita della struttura dei file
- Modello ML addestrato sulle minacce zero-day
Più motori sono meglio di uno
- Rileva quasi il 100% delle minacce informatiche
- Scansione simultanea con oltre 30 motori AV leader del settore
Fermare le minacce che gli altri non vedono
- Supporta oltre 200 formati di file
- Sanificazione ricorsiva di archivi annidati a più livelli
- Rigenerare file sicuri e utilizzabili
Rilevamento del vero tipo di file per i flussi di lavoro critici per la sicurezza
- AI potenziata
- Rileva i tipi di file falsificati in pochi millisecondi
- Applicazione in linea senza perdita di prestazioni
Prevenire la perdita di dati sensibili
- Utilizzate modelli basati sull'intelligenza artificiale per individuare e classificare il testo non strutturato in categorie predefinite.
- Occulta automaticamente le informazioni sensibili identificate, quali dati personali (PII), informazioni sanitarie protette (PHI) e dati relativi al settore dei pagamenti con carta (PCI), in oltre 125 tipi di file
- Supporto per il riconoscimento ottico dei caratteri (OCR) nelle immagini
Rilevamento di malware evasivo con Sandboxing avanzato basato sull'emulazione
- Analizzare i file ad alta velocità
- Il motore sandbox anti-evasione estrae le IOC
- Identificare le minacce zero-day
- Abilitate la classificazione profonda delle minacce informatiche tramite API o integrazione locale.
Migliorare il rilevamento con le Threat Intelligence in tempo reale
- Correlazione di IOC, IP, URL e reputazione dei file a livello globale su oltre 50 miliardi di artefatti.
- Bloccare più velocemente le minacce emergenti
- Arricchire l'analisi a valle
Secure laSupply Chain Software
- Gestire i rischi associati al software open-source (OSS), ai componenti di terze parti e alle dipendenze.
- Garantire la trasparenza, la sicurezza e la conformità della base di codice.
Rilevare le vulnerabilità delle applicazioni prima che vengano installate
- Verificare la presenza di vulnerabilità note nel software prima dell'installazione
- Eseguire la scansione dei sistemi alla ricerca di vulnerabilità note quando i dispositivi sono a riposo
- Esaminare rapidamente le applicazioni in esecuzione e le loro librerie per individuare eventuali vulnerabilità.
Rilevamento immediato dell'origine geografica di un file
- Rilevare l'origine geografica dei file caricati, compresi PE, MSI e SFX (archivi autoestraenti).
- Analizzare automaticamente le impronte digitali e i metadati per identificare luoghi e fornitori soggetti a restrizioni.
Estrazione e analisi ricorsiva di file di archivio profondamente annidati
- Estrazione ricorsiva fino a una profondità configurabile
- Estrazione in un unico passaggio su tutti i motori
- Rilevamento e contenimento delle bombe negli archivi
- Supporto per archivi crittografati e protetti da password
Opzioni di distribuzione

Cloud Native
Deploy MetaDefender Core in your cloud environment for scalable, on-demand AI pipeline protection.
Integrates with cloud-based AI workflows via REST API, supporting elastic scaling for variable file ingestion volumes across LLM applications and RAG pipelines.

On-Premises
Full on-premises deployment for organizations requiring complete control over data and infrastructure.
Air-Gapped / High-Assurance
Air-gapped deployment with MetaDefender Optical Diode for hardware-enforced unidirectional data transfer.
Integrazioni
It scans at every stage, from file upload portals and RAG ingestion pipelines to CI/CD workflows used in AI model and chatbot development. The platform connects to existing enterprise AI environments, including cloud platforms such as AWS and Azure, without requiring changes to application logic or model infrastructure.
Where MetaDefender Core
Fits in the AI Stack
MetaDefender Core acts as the AI security gateway, inspecting and sanitizing content before file upload, before RAG ingestion, before tool execution, and before data crosses a trust boundary.
Protect AI Copilots Handling Sensitive Financial Data
Financial institutions using LLM-powered copilots for research, compliance, and customer service need to prevent sensitive data leakage and ensure that uploaded documents are free of embedded threats. Proactive DLP and Deep CDR™ Technology enforce content-level controls before files reach the model.

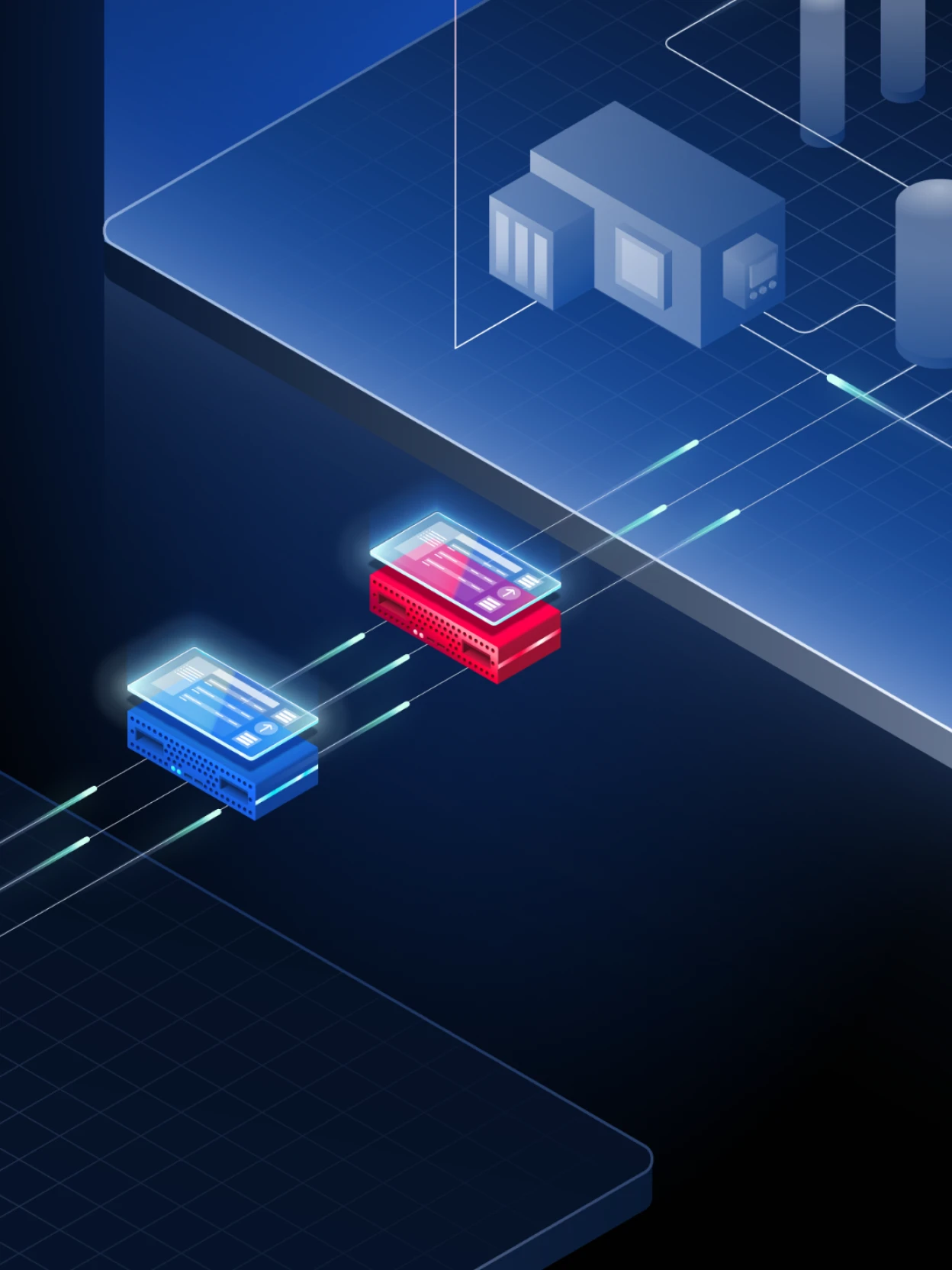
High-Assurance AI with Hardware-Enforced Isolation
Government and defense agencies require the highest levels of data assurance. MetaDefender Core sanitizes all content entering classified or sensitive AI environments, and MetaDefender Optical Diode ensures no data can flow back through the ingestion path — meeting strict cross-domain transfer requirements.

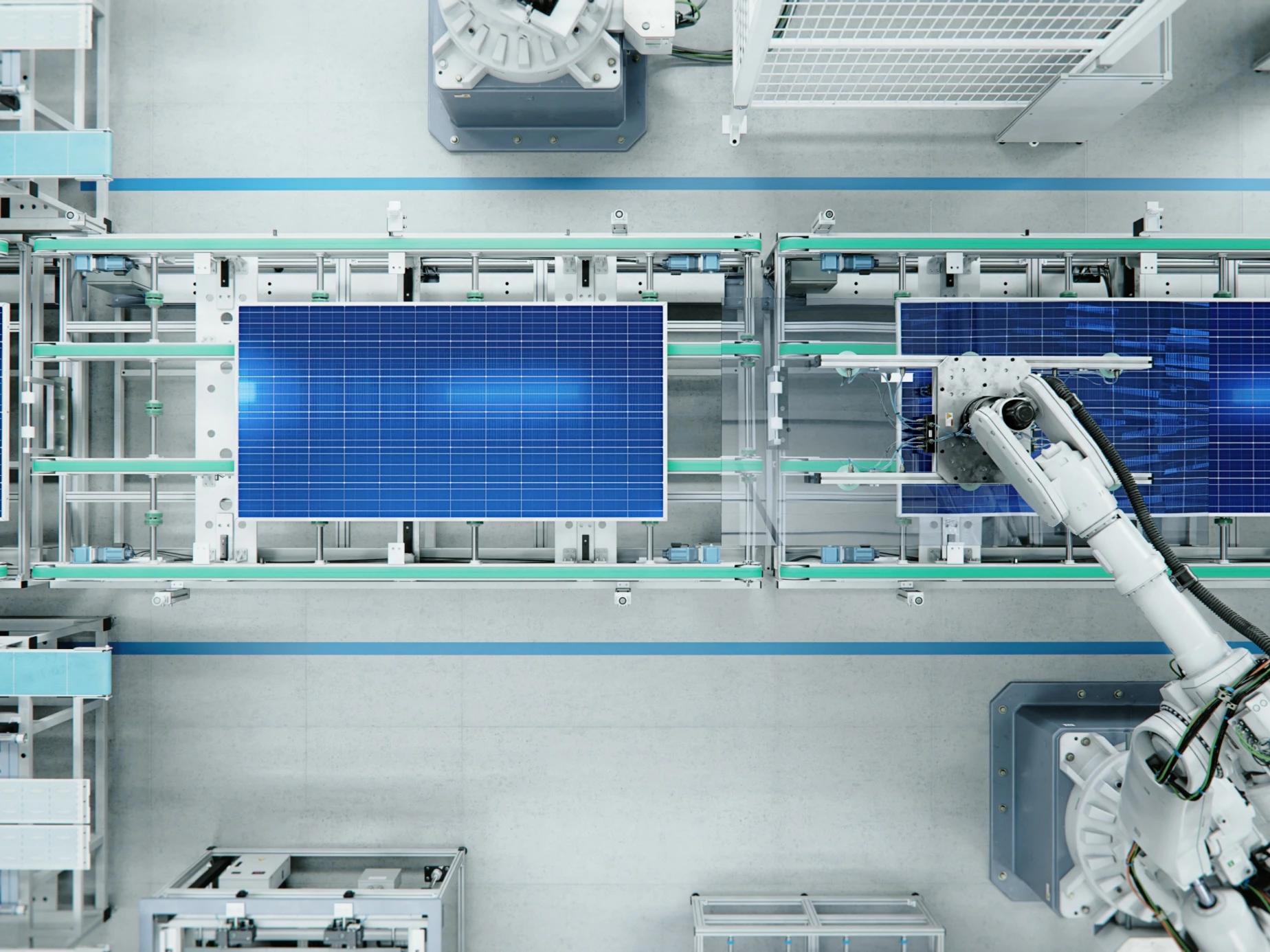
Secure AI-driven Analytics in Operational Environments
Manufacturers using AI for predictive maintenance, quality control, and supply chain optimization must protect against file-borne threats entering through data ingestion. MetaDefender Core provides policy-driven enforcement at every ingestion point, with air-gapped deployment options for isolated OT networks.
Secure AI Deployments Across OT and IT Environments
Energy and utilities organizations deploying AI for operational intelligence need to ensure that untrusted files and data feeds cannot introduce malware or manipulate models connected to operational technology networks. MetaDefender Optical Diode enforces one-way data transfer between IT and OT zones.

Risorse consigliate

Protezione delle pipeline di dati per l'IA e delle applicazioni basate su modelli di linguaggio di grandi dimensioni (LLM)

Software accelerato dall'intelligenza artificiale rende la sicurezza dei file la nuova linea di difesa contro gli attacchi informatici
Domande frequenti
MetaDefender Core supports over 200 file types including PDFs, Office documents, archives, images, media files, source code, and executables, covering the full range of content commonly ingested by enterprise AI systems.
Deep CDR™ Technology does not rely on detecting known threats. It strips all active content from files and reconstructs clean, usable versions, neutralizing both known and unknown malware, including zero-day threats.
Yes. MetaDefender Core inspects and sanitizes files before they are indexed into vector stores or retrieval systems, reducing the risk of RAG poisoning and long-term knowledge manipulation.
The MetaDefender Optical Diode is a hardware-enforced, one-way data transfer device. It physically prevents data from flowing back into a protected environment — required for defense, critical infrastructure, and any deployment where software-only controls are insufficient.
MetaDefender Core integrates via REST API or ICAP at any data ingestion point, including file upload portals, RAG pipelines, CI/CD workflows, and AI training data feeds. No changes to application logic or model infrastructure are required.
Yes. MetaDefender Core provides secure input validation, complete audit trails, file hashing, and logging that support compliance with the EU AI Act, Cyber Resilience Act, GDPR, HIPAA, and other emerging AI regulatory frameworks.
Yes. Proactive DLP scans for PII, PHI, financial data, and credentials. It also uses OCR to detect and redact hidden text within images and visual content that could bypass human review.
MetaDefender Core deploys cloud-native, on-premises, or in air-gapped architectures. For high-assurance environments, it pairs with the Optical Diode for hardware-enforced unidirectional transfer.